The spectacle that is Y Combinator's Demo Day took place for the Summer 2023 batch from September 6-7, 2023. Ten cybersecurity, privacy, and trust startups were among the 218 companies unveiled at the two-day event.
I have a soft spot for early stage startups, so here I am covering YC's cybersecurity startups for the fifth time. Like the previous four, this article is a quick analysis of every company from the industry in the Summer 2023 batch:
- Accend: A co-pilot for fintechs and banks to use when performing manual Know Your Customer (KYC) reviews.
- Affinity: A compliance training platform for companies in regulated industries.
- Corgea: Third party data security for sensitive workflows.
- Greenlite: AI agents for financial crime investigations.
- Kobalt Labs: Data privacy for generative AI.
- Remy Security: AI-automated product security reviews.
- SafetyKit: Replacing human trust and safety reviewers with AI language models.
- Sero AI: AI-powered content moderation for trust and safety teams.
- Trench: An open source fraud prevention platform for marketplaces.
- Xeol: A software supply chain security platform.
This time, I'm also including a look at Y Combinator's investment trends in the industry for the past five years. I haven't been covering YC companies for quite that long (since the Summer 2021 batch), but I've been doing it long enough to identify some trends. Let's start there.
Investment trends across batches
Our (current) no good, very bad economic conditions make things difficult for early stage companies. YC companies are no exception, despite the disproportionate advantage they get from being part of the best startup accelerator the world has ever known.
We're not here to rain on the parade, though. There are positive trends for cybersecurity, privacy, and trust companies that need to be talked about. I'll cover a few here, but this really could be an entire article (someday...).
Y Combinator is investing in cybersecurity companies at double its historical rate.
In YC's current era of smaller batch sizes, ten companies from the industry is still a healthy representation. Batches across the past three years have averaged 11 cybersecurity companies — a rate more than double the 4.5 company per batch average from 2019 and 2020.
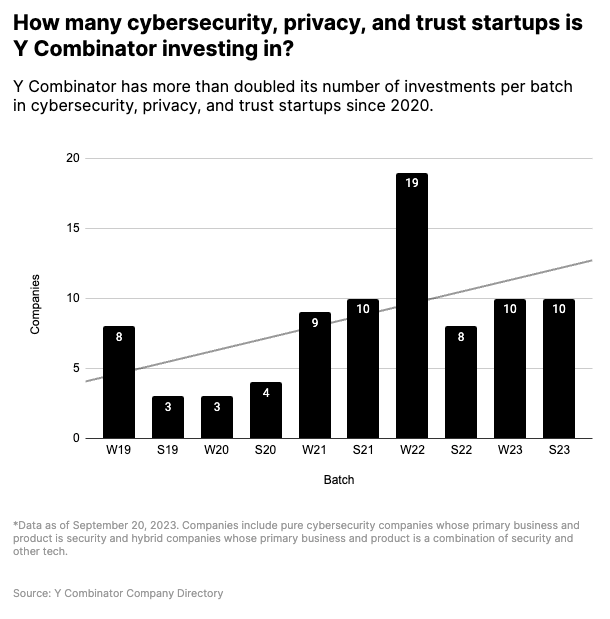
YC's consistently high investment rate is a good sign for cybersecurity companies, considering the ~40% reduction in overall batch size starting in Summer 2022. The reduction halved the number of startups from a 19 company spike in Winter 2022, but the average is still well above their historical trends.
Cybersecurity is still under 5% of YC's overall batch size.
Not to get greedy here, but an average of 11 companies per batch for the cybersecurity industry is still under 5% of the total batch size over the past five years.
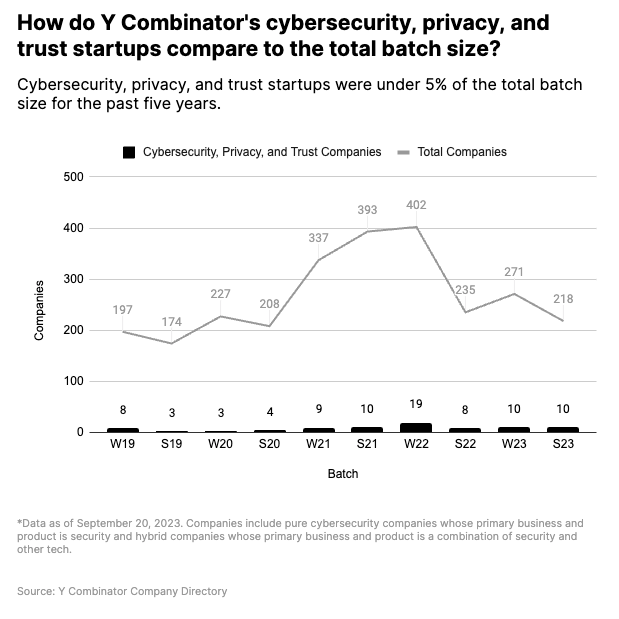
A 218 company batch at Y Combinator's standard deal (TL;DR, it's $500,000 per company) means they invested just over $100 million for the entire batch. Ten cybersecurity companies is $5.5 million of the total. That's a healthy amount, but our industry has also seen over 50 seed rounds of $5 million or more in 2023 alone (according to Crunchbase data).
YC generally funds companies at the earliest possible stage, so the companies they attract are naturally seeking lower investment amounts. When capital was easier to come by, it was easier for cybersecurity companies to bypass YC and raise higher amounts of capital from early stage venture investors. Times have changed, which could mean more (or higher quality) cybersecurity companies wanting to do YC.
Funding 10 cybersecurity companies at once (and ~20ish per year across both batches) is still a lot. The most active venture capital firms in cybersecurity average 10-ish investments per year (40-50 investments in a five year period, according to the Momentum Cyber Cybersecurity Almanac for 2023). This batch is further proof that YC continues to be one of the most prolific investors in cybersecurity, at least based on quantity.
80% of companies haven't raised additional financing yet.
You'd think being part of both Y Combinator and a seemingly recession-proof and well capitalized industry like cybersecurity would help companies raise funding. The current data says otherwise.
Similar to the Winter 2023 batch, only two of the 10 companies in this batch have raised additional funding outside Y Combinator's initial investment. According to PitchBook data, Corgea raised a small, early stage round in June 2023. SafetyKit raised a seed round led by First Round Capital in August 2023. That's it so far.
Other companies in this batch will raise funding, of course. However, we're clearly in a correction period from the days where YC companies had investments from top-tier firms at premium valuations weeks before Demo Day.
Accend
What does the company do?
Accend is building an automated workflow for fintech ops and compliance teams to make regulatory reviews more efficient and accurate.
Their current product is somewhere between augmentation and automation. Parts of the compliance process are automated, like generating standard regulatory reports for Customer Due Diligence (CDD) and Enhanced Due Diligence (EDD). Pre-defined workflows augment human reviewers to improve consistency and quality in the overall review process.
Where do they fit into the cybersecurity ecosystem?
It's a Fraud and Risk product. This category is somewhat adjacent to pure cybersecurity, but core security principles like identity and authenticity are fundamental to what the company is building.
What are their challenges?
The biggest challenge with automating high scrutiny (and high risk) processes is quality. For the product to deliver on its promises of saving time and reducing risk exposure, it needs to consistently produce better results than the humans it's (eventually) replacing.
At the company's current stage, quality is relative. Humans are still expected to review and sign off on the results. This is a totally reasonable ask. If the quality of the system-generated output is high enough most of the time, it still saves ops and compliance teams a lot of time (relative to starting from zero with no automation).
Over time, quality will get higher and results will get better. Manual reviews will get shorter and shorter, eventually reaching a point where humans are only reviewing a narrow set of exceptions and edge cases.
Why could this be a big company?
The big company version Accend is something like "the leader in compliance automation for financial services companies." Their current product is focusing on a relatively narrow set of use cases (as it should). Financial services companies have a lot of regulatory-driven paper pushing to automate. The surface area of opportunity for Accend is large.
From a growth standpoint, scaling alongside earlier stage fintech startups and (eventually) reaching enterprise financial services companies can help Accend become a big company. The model of selling to startups and scaling as they grow (as made famous by YC alums like Stripe and Brex) definitely applies here.
On the enterprise side, larger, more traditional banks will continue to do manual reviews until they need to cut costs or get hit with a large fine. Unfortunately, in banking, a lot of behavioral change is driven by regulators. One way or another, they'll eventually reach a point where they need to automate more of their compliance processes — a huge opportunity for Accend if the company can establish itself as a leader in the space.
Affinity
What does the company do?
Affinity is a training platform built for companies in regulated industries.
The product is unique because it's focused specifically on companies in regulated industries, not general security awareness training. It also manages training across multiple external parties (e.g. B2B customers), not just an internal workforce.
Where do they fit into the cybersecurity ecosystem?
Affinity is a Security Awareness company. Compliance is also a secondary driver.
What are their challenges?
Differentiation could be difficult in a relatively crowded security and awareness training market. The threat of substitutes for training content is high. In this market, it's hard to build a moat on content alone. The founders are clearly aware of this and know where to focus based on their previous experience building a buy now, pay later (BNPL) company.
Additionally, education and training isn't valued as highly by customers as flashier areas of cybersecurity. Many buyers view training as a commodity and shop for the lowest price. Affinity is trying to mitigate this by focusing on specialized training in the immediate proximity of revenue-generating business activities.
Why could this be a big company?
Positioning training close to revenue generation (on the external side) and risk reduction (on the internal side) is a unique insight. If Affinity can flip the narrative and turn compliance-driven training into a revenue driver, it can be a big company.
The market for Affinity's product is bigger than you might expect. PitchBook's analyst-curated fintech vertical currently tracks 9,455 companies. The broader market for regulated industries is even larger.
Also, don't sleep on the security awareness market. It has already yielded a (formerly) public company in KnowBe4, which was taken private by Vista Equity Partners for $4.6 billion in October 2022.
Corgea
What does the company do?
Corgea helps companies map and monitor the flow of sensitive data, including third parties. This visual is a perfect description:
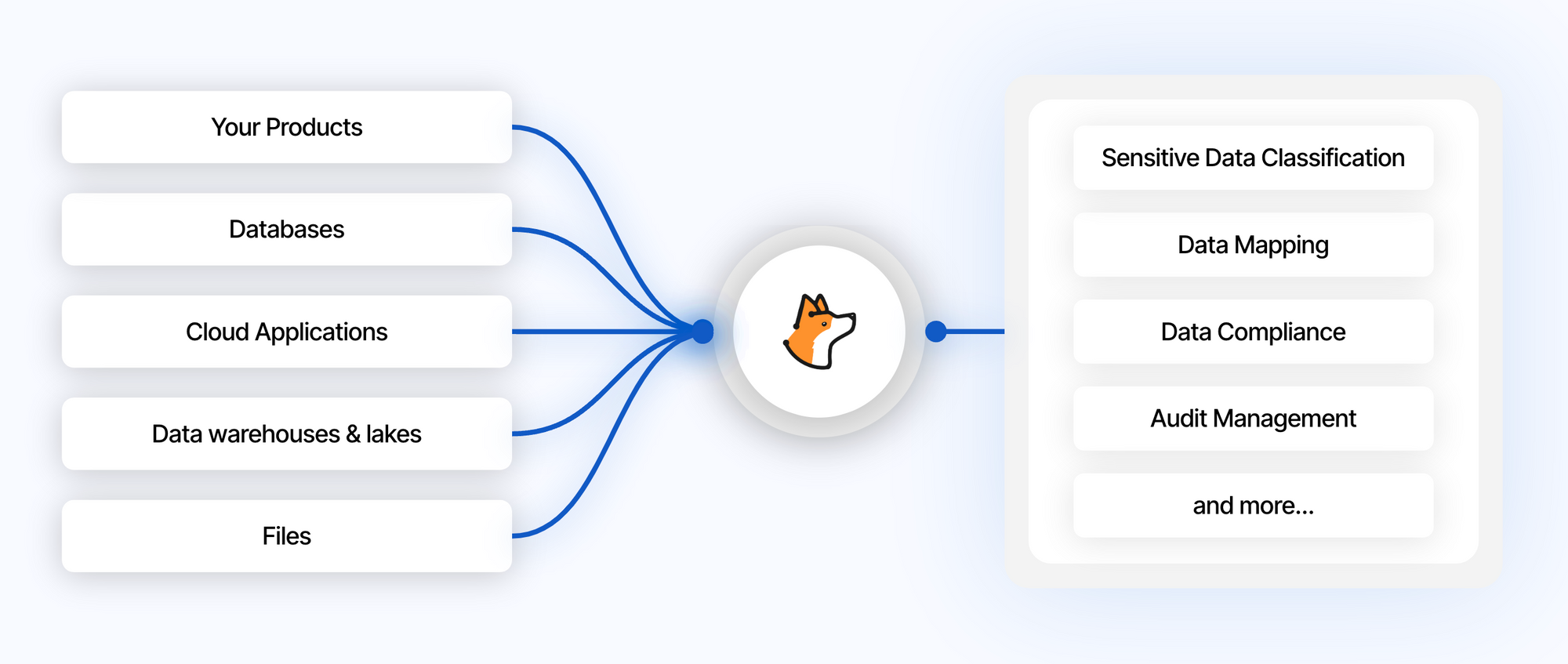
Corgea isn't your DLP product of a decade ago. It's a modern approach built for cloud-first companies.
Where do they fit into the cybersecurity ecosystem?
Corgea is primarily a Data Loss/Leakage Prevention product with a (slight) slant towards third party risk. It fits into the wider data security category — one of the most interesting spaces in cybersecurity right now.
What are their challenges?
Mapping data workflows is a hard problem to solve, especially when third parties are involved. Completeness and accuracy of coverage matter. Corgrea already has over 300 out-of-the-box connectors to SaaS apps and other data sources, which is a lot for an early stage company. Keeping up with integrations can feel like a never-ending treadmill, though.
Working with larger companies (mid-market and enterprise) is challenging for data security products. Larger companies with legacy apps may not be covered yet by out-of-the-box connectors. In the data security market, enterprise is the space of large, well-funded startups like BigID and OneTrust. Corgea doesn't need to compete for enterprises right now, but it's a challenge they'll face with growth.
Why could this be a big company?
Data security is one of the most active markets in cybersecurity right now across financing, M&A, and innovation in general. This quote from my discussion with Amer Deeba, CEO and co-founder of Normalyze is the punch line:
Data security is going to be a huge category on its own with a big focus on the cloud.
DSPM is the future of data security — how to manage data from a security perspective, how to classify it, and how to secure it on an ongoing basis. It's a huge category that's going to consolidate many other cloud security tools around it.
Evidence of financial and strategic interest in data security is clear. Recent acquisitions from strategic buyers include Polar (by IBM), Laminar (by Rubrik), and recent speculation about Palo Alto Networks acquiring Dig Security. Early stage data security companies have also raised over $500 million from investors (according to Momentum Cyber research).
Greenlite
What does the company do?
Greenlite builds AI agents for fintech compliance teams. The product directly takes aim at outsourced analysts: "Greenlite can help you scale your compliance operations with AI instead of outsourced teams."
If this sounds similar to Accend, you're on the right track. Both companies are solving a similar problem — routine AML and KYC compliance tasks. The difference is in their approach. Greenlite is more agent-based, leaning on AI to execute tasks. Accend is more workflow-based, relying on defined processes to execute tasks.
It's common for Y Combinator to invest in competing companies, both within the same batch and across previous batches.
Where do they fit into the cybersecurity ecosystem?
Similar to Accend, Greenlite is a Fraud and Risk product.
What are their challenges?
Greenlite faces the same challenges as Accend, plus an additional one because of their heavy reliance on AI. The product's results are heavily dependent on the abilities and limitations of LLMs and their ecosystems of tooling. Any internally developed, domain-specific AI/ML models will also require a lot of training data to reach a high level of accuracy.
Using AI is also a huge opportunity, of course. LLMs and AI tools are improving exponentially by the day. Internal models are getting easier and easier to build. Greenlite has an opportunity to turn these challenges into insurmountable strengths with enough time and training data.
Why could this be a big company?
Greenlite's YC launch shared a damning stat from McKinsey:
Critically, the productivity of these AML teams are low. McKinsey estimated that as little as 15% of an AML investigator’s time is spent actually investigating. Manual processes, administrative tasks and limited working hours leave backlogs to grow, increasing risks of a major fine.
Compliance reviews are a necessary evil for fintech companies. They're never going away. Doing reviews well is expensive and slow. Doing them poorly is an existential business risk — no company wants to be fined or shut down by a regulator.
Making compliance reviews both fast and accurate directly unlocks customer growth (by improving customer experience) and reduces risk exposure (by catching and preventing fraud). It's the fintech equivalent of augmenting and automating the SOC, which is central to the success story of Palo Alto Networks.
Solving the problem of compliance automation is a huge opportunity. The winner will be a big company, or at worst have a nice exit.
Kobalt Labs
What does the company do?
Kobalt Labs is an API for securing sensitive data, both as an input to and output from LLMs.
Their approach is roughly similar to JumpWire and Sarus from the Winter 2022 batch, but designed specifically for LLMs and the dynamic nature of their inputs and outputs.
Where do they fit into the cybersecurity ecosystem?
Kobalt Labs is a privacy and data protection product built specifically for LLMs. You could also argue it's in the AI Security market if you view this as a standalone domain in cybersecurity.
What are their challenges?
The (still very nascent) AI security landscape is becoming more crowded by the day. The popularity of LLMs have brought lots of brainpower, capital, and new products to the security side of the space. As with every embryonic stage market, there's a lot of uncertainty, risk, and competition.
There are also the practical challenges of usage and adoption. An API-focused approach requires everyone in the company to actually use the API. Most LLMs make it easy for employees to go rogue and start using them without company (or security) approval. Even if people are using company-sanctioned LLM accounts, there are still political barriers to overcome before a security solution is universally adopted.
Why could this be a big company?
The AI attack surface is already large, rapidly evolving, and remains relatively exposed. AI companies are aware of security and privacy challenges. Both are higher priority than usual, partly in favor of gaining enterprise customers.
AI companies are well funded and have other difficult problems to solve. We're likely to see them using part of their cash reserves on acquiring AI security products that can unlock customer growth and give their platforms an advantage over competitors.
If Kobalt Labs can become the go-to solution for LLM security and data privacy, they can be a massive company.
Remy Security
What does the company do?
Remy Security uses LLMs to help security teams do product design reviews. Security design reviews are (should be?!) an early step of the overall development process — well before later stage application security testing and pentesting.
Remy Security's product augments a reviewer and helps get some basic analysis out of the way before human expertise is needed.
Where do they fit into the cybersecurity ecosystem?
Remy Security generally fits into the Security Architecture category. They're also directly related to the Application Security market, but in a different way than traditional products that deal directly with code.
What are their challenges?
Reviewing software product designs is a lot less straightforward and repetitive than the compliance reviews Accend and Greenlite are doing. The nature of product security reviews is different, and the nuances matter.
Compliance reviews under AML and KYC are required by external regulators. Product security reviews are not. They're completely optional, even though any decent security practitioner would tell you it's a good idea. The bad part about being optional is companies can skip product reviews entirely, or rubber stamp them and move on.
Similar to Greenlite, the product's heavy reliance on LLMs is subject to the limitations of LLM performance and accuracy. The Remy team makes it clear a human is expected to be involved in the review process at some point. This is exactly the right approach for an early stage product and helps keep customer expectations in check.
Why could this be a big company?
We hear "shift left" all the time (okay, too much). This is one of the first attempts at applying a security product to the design/architecture phase. Historically, design is a process-oriented phase. Building a product to help with this is a pretty revolutionary idea.
The upside is Remy's product can help increase the number of security design reviews that get done. They're using new technology to expand the market for security design reviews. And, if we're being brutally honest, that market should be a lot bigger than it is today.
If Remy can materially expand the quantity and quality of security design reviews, they can be a big company. This could also be a nice acquisition for larger, well-funded application security companies looking to broaden their platforms into new areas.
SafetyKit
What does the company do?
SafetyKit is using LLMs to augment and replace trust and safety reviewers. The product executes customer-specific workflows to identify and make decisions about content moderation.
Where do they fit into the cybersecurity ecosystem?
SafetyKit is a Trust and Safety product.
What are their challenges?
SafetyKit shares many of the same challenges as other trust and safety startups from previous batches. Content moderation is a somewhat unique challenge faced by companies with lots of user generated content once they reach scale. I summarized the challenge when writing about Cinder, a company from the Winter 2022 batch:
Finding customers at the right level of traction and scale to require more advanced trust and safety operations is potentially tricky. Small companies with seed funding or earlier are usually still seeking traction. This doesn't leave much room to focus on problems outside of growth — trust and safety being one such problem.
I also called out the variety of content moderation problems companies face:
There is also a lot of variety in this space. Trust and safety threats and problems vary by company and by industry, as do the processes for solving them.
SafetyKit does a nice job of addressing the variety by allowing customers to define their own company-specific workflows and rules. The product also provides clear reasoning about moderation decisions made by the platform (lots more detail about this in their YC launch).
Why could this be a big company?
Content moderation jobs meet all the criteria of jobs that should be automated. Here's a real example of a job posting from Upwork:
Veriswap isn't your prototypical user generated content giant like Facebook, Twitter, or Airbnb. It's a marketplace for trading sports cards (just like I used to do in person as a kid). Seems innocuous enough, but guess what?! They still need content moderation.
The opportunity for SafetyKit is to help the (growing) long tail of businesses who have user-generated content. Giants like Stripe and Airbnb (where SafetyKit's founders previously worked) aren't necessarily the ideal customer. They're on the front of the curve with the scale and resources to build their own solutions.
It doesn't make sense for companies like Veriswap to build a trust and safety platform (let alone an LLM-powered one) from the ground up. Content moderation is not their core business, as shown by the meager $5-12 hourly rate they're offering for the role above. They're better off integrating a product like SafetyKit and eliminating their entry level roles for good.
From a broader market standpoint, trust and safety has had some interesting acquisitions in the past year. Spotify acquired Kinzen in October 2022 to help address platform safety issues. ActiveFence acquired Spectrum Labs in September 2023. ActiveFence has raised over $100 million at a $500+ million valuation, according to TechCrunch. It seems likely a big company is going to emerge from this space.
Sero AI
What does the company do?
Sero AI is an AI-powered content moderation platform for trust and safety teams. This should sound familiar. Both Sero AI and SafetyKit are solving a very similar problem.
The main difference I can see between the companies is their approach to implementing AI. Sero AI focuses more on machine learning. SafetyKit uses LLMs.
Where do they fit into the cybersecurity ecosystem?
Sero AI is a Trust and Safety product.
What are their challenges?
Sero AI faces the same challenges as SafetyKit and other trust and safety startups from previous YC batches.
Why could this be a big company?
All the same opportunities for SafetyKit apply to Sero AI. The differentiator for both companies is their use of AI. Workflows matter too, but AI might end up being the difference in this market.
Trench
What does the company do?
Trench is an open source fraud prevention platform for marketplaces. The product brings together reviews for buyers, sellers, and payments — along with the services and data needed for the reviews — into a centralized decisioning point.
Where do they fit into the cybersecurity ecosystem?
Broadly speaking, Trench is a Fraud and Risk product. It's focused on the fraud side and relies heavily on identity proofing and device fingerprinting techniques to aid the verification process.
What are their challenges?
There isn't a "one best way" for ecommerce and marketplace businesses to prevent fraud. The result is a wide variety of approaches and products that solve specific use cases (or categories of them). And basically all the financial services giants are in this market.
Sift is a YC company from the Summer 2011 batch now valued at over $1 billion (from its latest financing round in 2021). Large financial services companies have fraud prevention products (via acquisition):
- American Express: Accertify (acquired in 2010 for $150 million)
- Equifax: Kount (acquired in 2021 for $640 million)
- LexisNexis: ThreatMetrix (acquired in 2018 for $817 million)
- MasterCard: Ekata (acquired in 2021 for $850 million)
- TransUnion: TruValidate (rebranded product from acquisitions of Neustar for $3.1 billion and Sontiq for $638 million in 2021)
- Visa: Cybersource (acquired in 2010 for $2 billion)
You could argue some of these products are entering "legacy" territory, which is part of the opportunity for Trench.
Why could this be a big company?
Building an open source product was a strategic decision. This statement from Trench is a contrarian point of view in the very closed source world of fraud platforms:
Fraud vendors can't solve fraud for you. Every business eventually needs to build something in-house.
Trench has a strategic advantage by taking a completely different approach and going open source. From an industry standpoint, the scale of the acquisitions (several listed earlier) by strategic buyers is massive. If Trench can become the equivalent of GitLab for fraud platforms, they can become a big company.
Xeol
What does the company do?
Xeol is a software supply chain security platform. Its main differentiator is a contextual graph that allows companies to ask specific questions about usage enforce policies.
Where do they fit into the cybersecurity ecosystem?
It's a Software Supply Chain Security company.
What are their challenges?
The supply chain security incidents we've seen this decade have attracted some of the best talent in the industry. Investors joined the party this year, and financing picked up. It's now a busy and competitive market.
Endor Labs raised a $70 million Series A last month, which is one of the largest early-stage cybersecurity funding rounds in 2023. They've raised a total of $95 million. Chainguard, FOSSA, and other startups also compete in this market.
Bigger cybersecurity companies are coming, too. Major acquisitions and convergence are happening as cloud and application security companies move towards full CNAPP platforms. For example, Snyk acquired Enso Security in June 2023 for its software supply chain features.
Why could this be a big company?
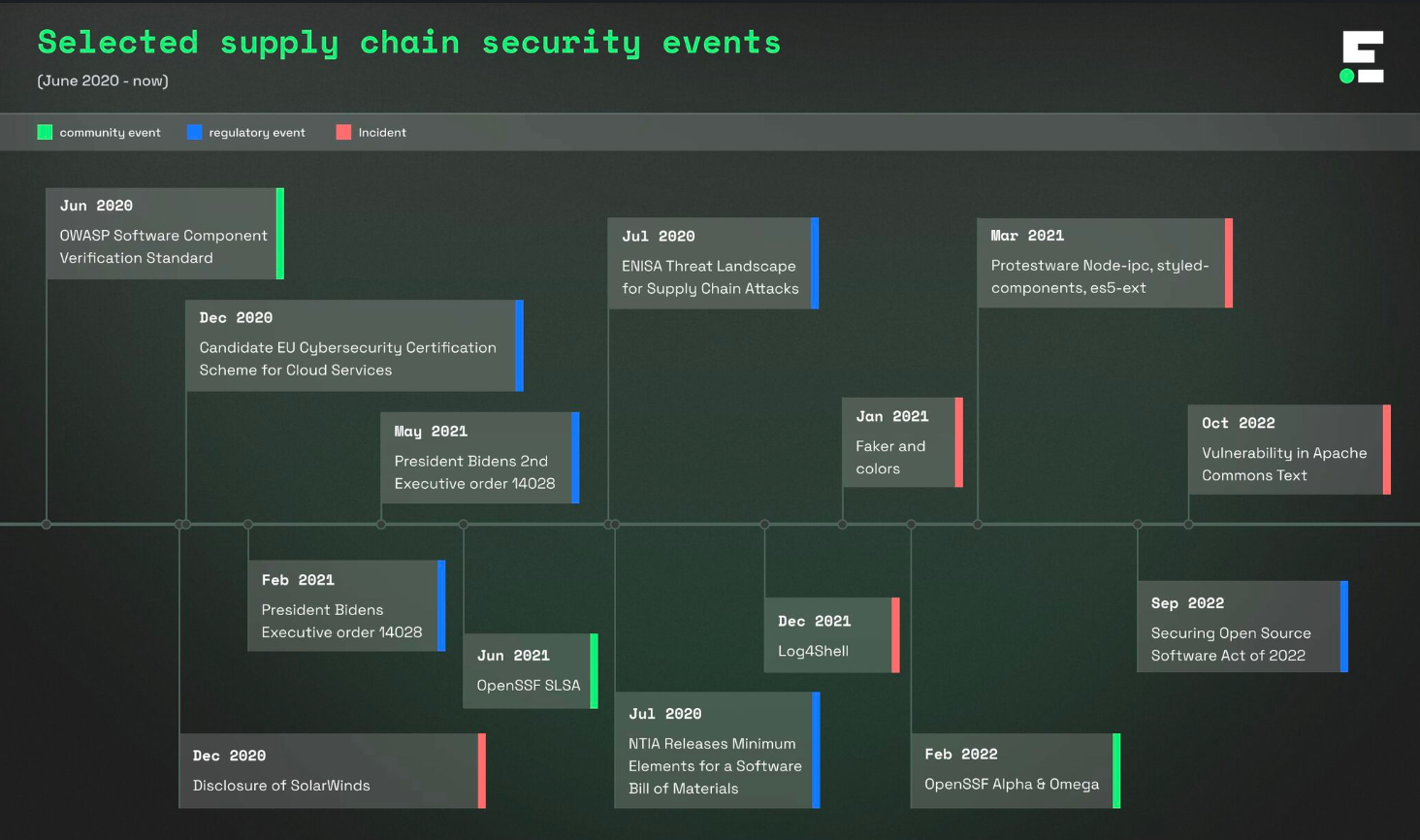
Varun Badhwar, the Founder and CEO of Endor Labs, shared a nice timeline of events that explains the ongoing series of serious software supply chain security incidents:
We're seeing a lot of new ideas, but this market is still in the early innings. If Xeol can build interesting tech, it's going to attract interest from strategic buyers looking to extend their application security platforms. If software supply chain security continues to be a serious problem, it's possible a large standalone company could emerge.