What began as a presumptive funeral ended as a tour de force from the world's largest cybersecurity company. When Palo Alto Networks set its Q4 2023 earnings release for a Friday afternoon, people had questions. Questions led to investor fears about poor results and lower guidance. Fear became action, which led to a drop in PANW's stock price:
Why is $PANW struggling? $FTNT the answer, or is it something more disturbing?
— ARMR Report (@BretRosenthal) August 16, 2023
IBD weighs in...
""Earnings for PANW stock are due after the market close on Friday, and will be followed by an extended call with Wall Street analysts.
Palo Alto stock plunged on Aug. 2. That's when… pic.twitter.com/e4GW0JGaTc
Rampant speculation took off from there, including "rumors" about CEO Nikesh Arora's impending resignation:
Rumor is Nikesh Arora may be stepping down but who really knows
— R B (@Slushe232) August 16, 2023
This bizarre sequence of events set the stage for the spectacle that was Palo Alto Networks' Q4 2023 earnings call. I've never seen anything like it in cybersecurity. The uncertainty leading up to it, followed by the unexpected and thoughtful narrative about the future of the company and the industry was quite the turn of events. Nikesh Arora even acknowledged how unique the situation became:
Our choice of Friday has definitely made us the topic de jure these past two weeks and has made for some very interesting reading of all the analyst notes.
To say this stunt (intentional or not — probably intentional) generated attention is an understatement:
We have 5.5k people dialled into our call. Average attendees last 5 years are about 1k. Not sure what to make of this. Someone just educated me on "Friday Night Lights". Thanks all for working with us on this.
— Nikesh Arora (@nikesharora) August 18, 2023
Palo Alto Networks delivered in a spectacular way, just like it's been doing for the five years (and counting) of the Nikesh Arora era. Despite several bear-ish analyst estimates and (especially) the rampant speculation about doomsday scenarios, the Q4 and FY23 earnings were just fine, as were FY24 projections.
The real story is the vision Arora and team laid out for the future of Palo Alto Networks and the cybersecurity industry. It's rare for a company to articulate such a definitive point of view. It's even more rare for them to do it on a Friday afternoon earnings call. And it's exceptionally rare for the point of view to be so outstanding.
So, yes, the event was technically an earnings call — but the implications are so much deeper. Understanding Palo Alto Networks' point of view is a dynamic reflection on several of the most important themes driving the future of the industry.
Platformization as a strategic advantage
A foundational idea for everything Palo Alto Networks is doing (and wants to do) is platformization. If you're averse to buzzwords, don't be put off by the term. I'd argue they're using it in the purest sense of the word: integrating a complex set of products and features into a platform with unified data and management. The payoff is an end-to-end platform greater than the sum of its parts.
There's an important distinction between "platformization" and "consolidation." Many people in the industry, including other large cybersecurity companies, have been talking a lot about consolidation for the past few quarters. In this context, they're referring to customers consolidating the number of security vendors they work with. Vendor consolidation is about cost savings, not value.
The drivers for platformization are very different. It's barely the same thing as vendor consolidation. Platformization has little to do with cost savings. It may result in consolidating products and vendors, saving money as a byproduct. The driver is better security outcomes and value for companies who use the platform.
What does this distinction mean in practice? Consolidation ≠ platformization. Just because you're buying multiple cybersecurity products from a single company doesn't mean the products are integrated or work well together.
Platformization goes beyond consolidation. It's an intentional set of activities to integrate products and unlock value that isn't possible without the integrated platform. It's a flywheel effect — small, incremental wins (new features and modules) accumulate over time, creating increasingly better and more valuable results.
The Palo Alto Networks leadership team did a good job explaining the challenges of disparate products and making their own case for the advantages of platformization. From Nikesh Arora:
...five years ago, we had customers who had more cybersecurity vendors than they had IT vendors. And it was a customer's responsibility to take these vendors, deploy them across their infrastructure, make them work together to deliver security outcomes.
You're expecting 2,000 customers out there in the Global 2000 or possibly tens of thousands of customers having security experts trying to stitch together products made by fast growth cybersecurity companies, which are deeply technical and trying to figure out how to correlate what one vendor saw or one set of vendors is telling you versus another. It just seemed like a problem that could not be solved.
But over the last five years, you've seen that starting to stitch these together, starting to take this disparate solutions for security, trying to provide them in a common fabric has actually allowed us to deliver better security outcomes.
And we've proven that by doing that in a way, they are -- each of those pieces work in a best-of-breed fashion are leading in their own category. However, they're better together in the platform.
More from Chief Product Officer Lee Klarich:
Everything we do is integrated. It's designed to solve hard problems through integration that cannot otherwise be solved with point products. And that combination enables our platforms to be real time and enable real-time security outcomes for our customers.
You could ask, "What's wrong with point products? We've been doing that forever in cybersecurity." There's also a stigma around monolithic platforms: the individual products making up the platform aren't as good as point solutions. I thought Lee Klarich's explanation of the tension was insightful:
...prior attempts to do this generally required a tradeoff for the customer. It was the capabilities that were delivered on their attempts to do a platform where not industry leading. And so, the customer had to make a tradeoff between, worse capabilities, but in one place, or best-in-class capabilities, and that's a hard trade off in cybersecurity. That is one thing that we're not asking our customers to do. We're making sure that everything we do is industry leading on its own.
The second thing we're doing is making sure that when we integrate it, they're actually integrated together in solving hard problems that can't be solved as standalone capabilities. So, we're it's not just about consolidation, although that's a clear value. It's about delivering technical outcomes through the integration that cannot be achieved otherwise.
Building a platform with best-in-class, industry-leading capabilities is trying to have your cake and eat it, too. It's difficult to pull off and powerful if it works. Palo Alto Networks is one of the few (perhaps the only?) cybersecurity companies capable of building a best-in-class platform across multiple product domains at scale.
Klarich's second point about the value of an integrated platform is also important. There's a reason cybersecurity services is an $80 billion market (according to PANW on this earnings call). Integrating security products is difficult and expensive. Being intentional about integrating the product up front instead of leaving it to customers to figure out for themselves is a game changer, even if the drudgery of systems integration doesn't excite you.
Integration is just the beginning. Unlocking the ability to solve security problems that aren't possible without an integrated platform is revolutionary. It's not possible to detect attacks reliably, and certainly not proactively, without a common data foundation and set of detections running on top of it. This is just one example — we're all still figuring out what's possible if we have an integrated platform to start with instead of chasing our tails trying to integrate everything.
Longer term, Nikesh Arora played out the impact of platformization even further, predicting the emergence of a standard security platform in the next decade:
...in the next decade, we will see sort of a standard platform for security out there, just the way we've seen platforms in CRM or we've seen platforms in HR, as you've seen platforms and financial sort of software.
We think it's time that in the next decade, we will see a security platform in our future, which just works for our customers, and the customers are not spending time integrating multiple vendors trying to stitch their own...that's the only way we're going to get to the future that we need for real-time and AI-based security.
You have to imagine a bit, but if you're optimistic, it's clear how this vision is possible. The reason it's hard to envision a standard platform for security is because it's really hard to build. Nikesh Arora and Palo Alto Networks are doing the cybersecurity equivalent of building Singapore: re-imagining everything from the ground up and pushing the boundaries of what's possible.
Can they pull it off? Time will tell — but you have to admire the audacity of trying.
Making real-time security a reality
Real-time security underpins the idea of platformization. Nikesh Arora summarized it nicely:
The idea that as something is happening, you're able to analyze it real time, on the fly and understand it's good or bad. It is reducing the noise of security in the industry by eliminating all these super close alerts or the bad signal to noise ratio.
As an industry, we've been talking about the idea of real-time security in various shapes and forms for a long time. Concepts like adaptive authentication, continuous compliance, and plain ol' antivirus scanners are all variations of the same paradigm.
Again, don't get lost in the buzzword here — the underlying idea is important. Nikesh Arora explained it like this:
What we think lies ahead is the need for security to stop bad actors mid-flight, real-time, as it's happening... What we still aren't good at as an industry is being able to figure out unknowns and stop them before they happen.
To do that, it requires a fundamentally different way of thinking about security... And that is the idea of having stitched products that work from end to end.
For as long as cybersecurity has existed (and longer), we've been trying to close the gap between when something bad happens, when it's detected, and when it's mitigated. Formally, it's the definition of MTTD and MTTR. Nikesh Arora's prediction is a shift towards results, outcomes, and speed:
It will no longer be about putting a bunch of sensors and thinking about hygiene and security policies. It will be about how do you stop a bad act. And we'll talk more about this because today, the mean time to fix a bad act...is four to six days. That's not acceptable. This thing will have to go down to minutes and near real time.
This anecdote aligns perfectly with the shift from promise-based to evidence-based security. Declaring something as "secure" isn't good enough anymore. We have to prove it's secure and do it in real time.
The challenge with real-time security has always been "how?" As he does, Nikesh Arora took a strong point of view in answering the question:
Now we sit at a point where everybody is talking about AI. And actually, that is the solution. The solution is to make sure you ingest large amounts of data, you analyze them on the fly, and you're able to deliver superior security.
At a high level, the "how" is platformization and AI. Anyone who is even mildly technical is likely both intrigued and unsatisfied by this answer. Gonen Fink to the rescue:
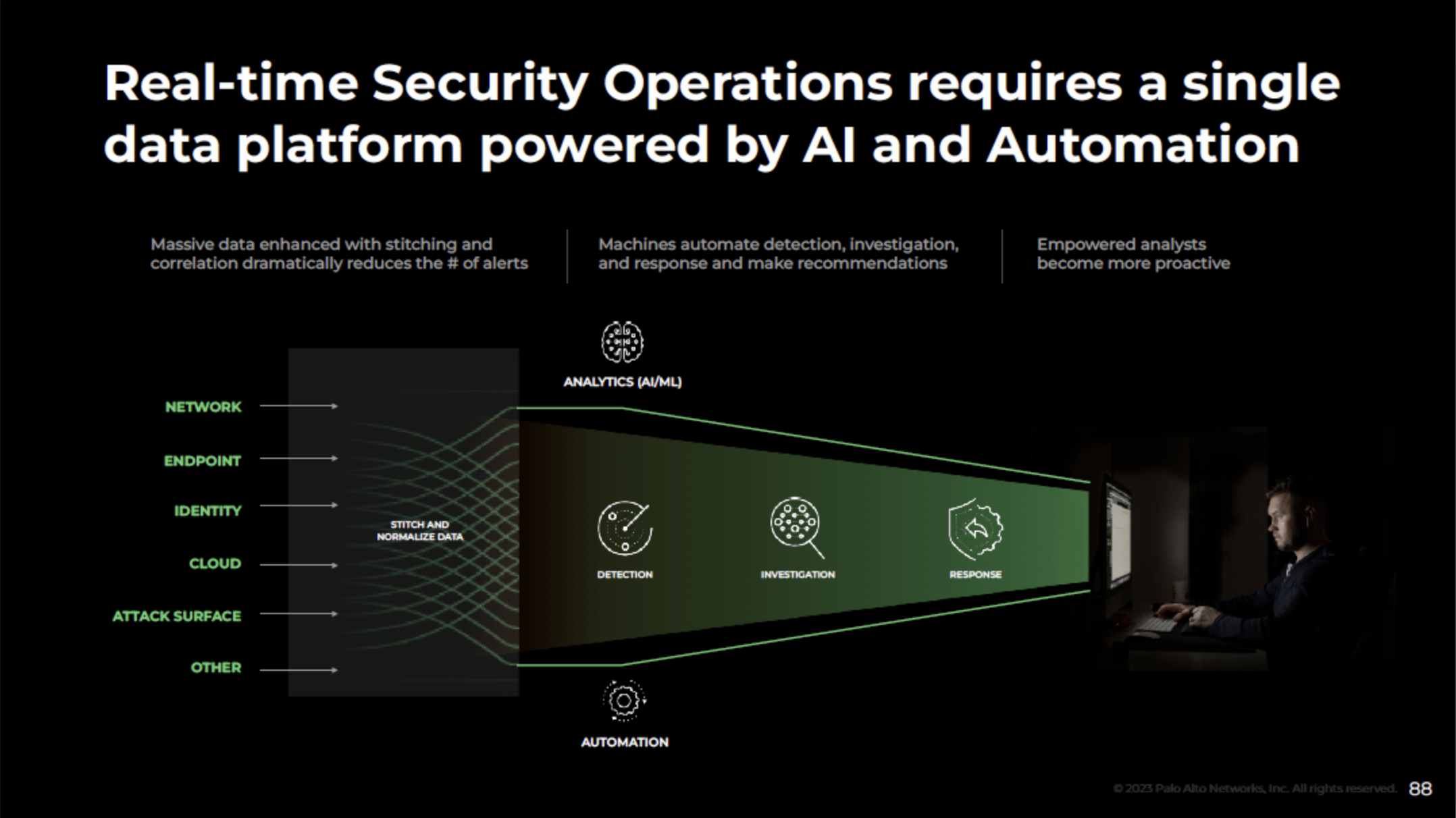
We need to replace this fragmented architecture with a unified single floor architecture. We need to replace multiple products that collect data with a single data platform and silo detection tools with an AI engine that is trained on a full data center. And then automation should be natively integrated into the flow rather than being placed as an afterthought.
Here's the same idea in visual form:
Building a real-time security platform like this is a tall order. But, they're right: we do need a fundamental transformation in security operations. Palo Alto Networks is all in on building towards this future. According to Nikesh Arora, it could be within reach:
We have to make sure every platform that we have continues to grow and continues to get more and more ubiquitous with our customers, at the same time, also stitches these things together. So we believe in the next five to 10 years, we're going to see this shift, which is going to be palpable.
Getting to a point anywhere close to real-time security across a company's entire security estate is a breakthrough. Skeptics may think it's impossible. They might be right, but these are the shots you need to take when you're trying to be the first $100 billion cybersecurity company.
Convergence of cloud and application security
The convergence of cloud and application security isn't a totally new idea, but we're definitely still in the early innings. This macro-level trend underpins a large part of Palo Alto Networks' strategy. They're one of a few companies with the combination of scale and innovation required to win.
Gartner's term for the convergence of cloud and application security is Cloud-Native Application Protection Platform (CNAPP). Here's how they define it:
CNAPPs address the full life cycle protection requirements of cloud-native applications from development to production.
First, the bad news: building a full CNAPP is really hard. In practical terms, building a CNAPP means performing basically every security function across development, build (CI/CD), and production for most of the stack (apps, workloads, networking). In market terms, building a CNAPP requires combining 5-10 other markets into a single platform.
Gartner's latest Market Guide for Cloud-Native Application Protection Platforms has a graphic that explains the situation quite well:
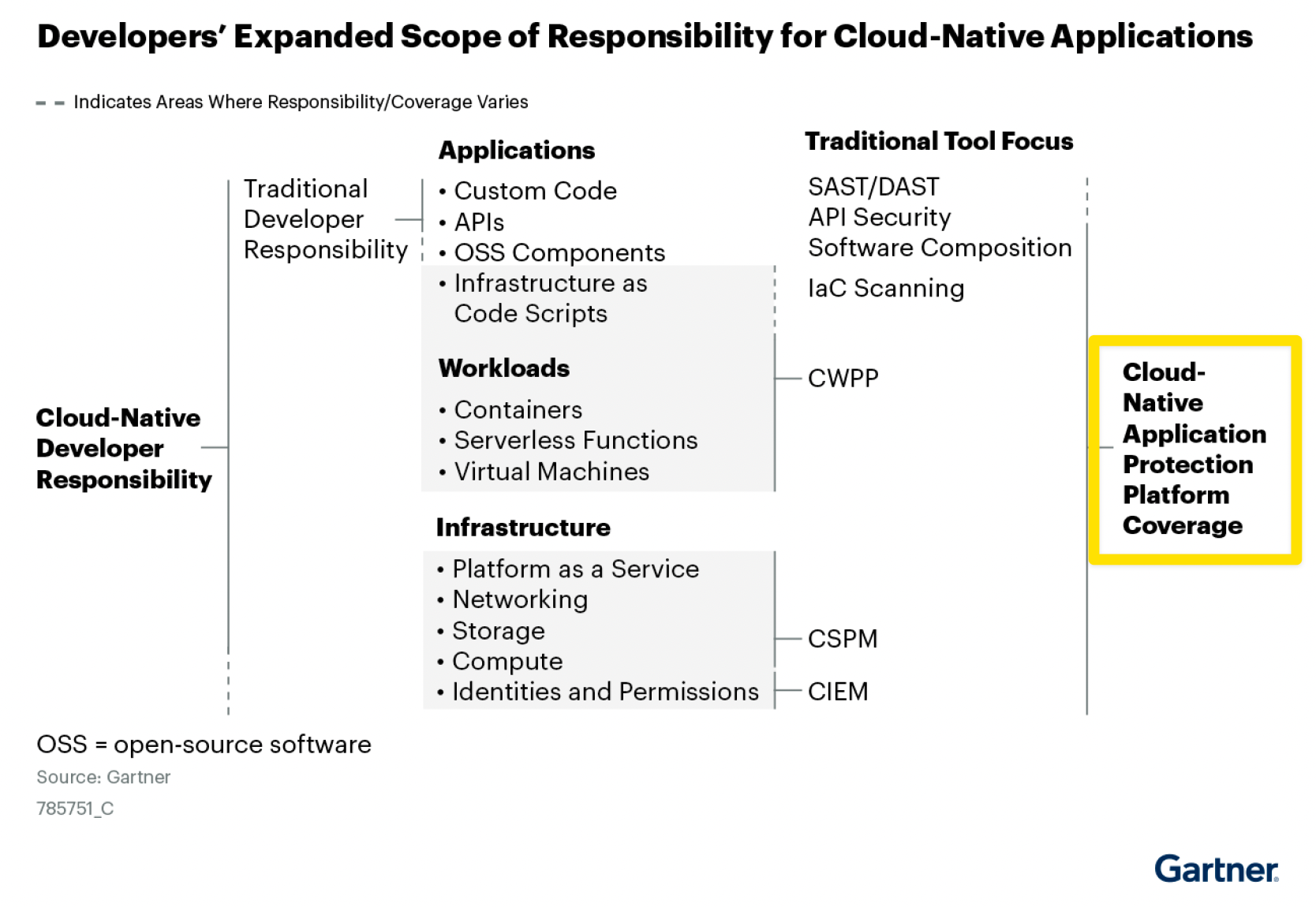
Unsurprisingly, no company has accomplished the massive feat of building a full CNAPP yet. From Gartner:
No single vendor delivers all of the capabilities [of a full CNAPP] today. CNAPP offerings are emerging from multiple providers, often from different starting points.
Gartner doesn't do Magic Quadrants for emerging markets like CNAPP, so Palo Alto Networks is listed alongside several other companies as a "representative vendor." Among the representative vendors, Palo Alto Networks is one of the furthest along the path to offering a full CNAPP.
Here's how Palo Alto Networks described the problem space during the forward-looking session of the earnings call (from Ankur Shah):
In the code phase, there are about half a dozen different tools to scan security posture. In the infrastructure layer, you have yet another set of tools. And finally, in the run time, you have tools for cloud workload protection, network security and application security. Now this is not the right approach to solving this problem for two reasons: number one, each of those tools lack the context. So the customers have to stitch all of that together.
And the second thing is, like Lee described, there are 33 million developers and a really few security professionals who understand code and cloud. This is a battle that the security team simply can't win with this specific approach.
We believe there is a better approach. And that's the approach that we have been steadfast in executing over the last four years, and that is an integrated code-to-cloud platform approach that can help customers prevent risks, and breaches in near real time.
In Palo Alto Networks terminology, the convergence of application and cloud security is called "code-to-cloud." Modules for CNAPP and beyond fall under the Prisma Cloud product umbrella. Their "Code-to-Cloud Platform" approach is a specific example of the platformization and real-time security concepts we talked about earlier. Here's how it works:
Prisma Cloud does that today by scanning security vulnerabilities at each phase of the application life cycle and also have runtime protection to prevent breaches in runtime.
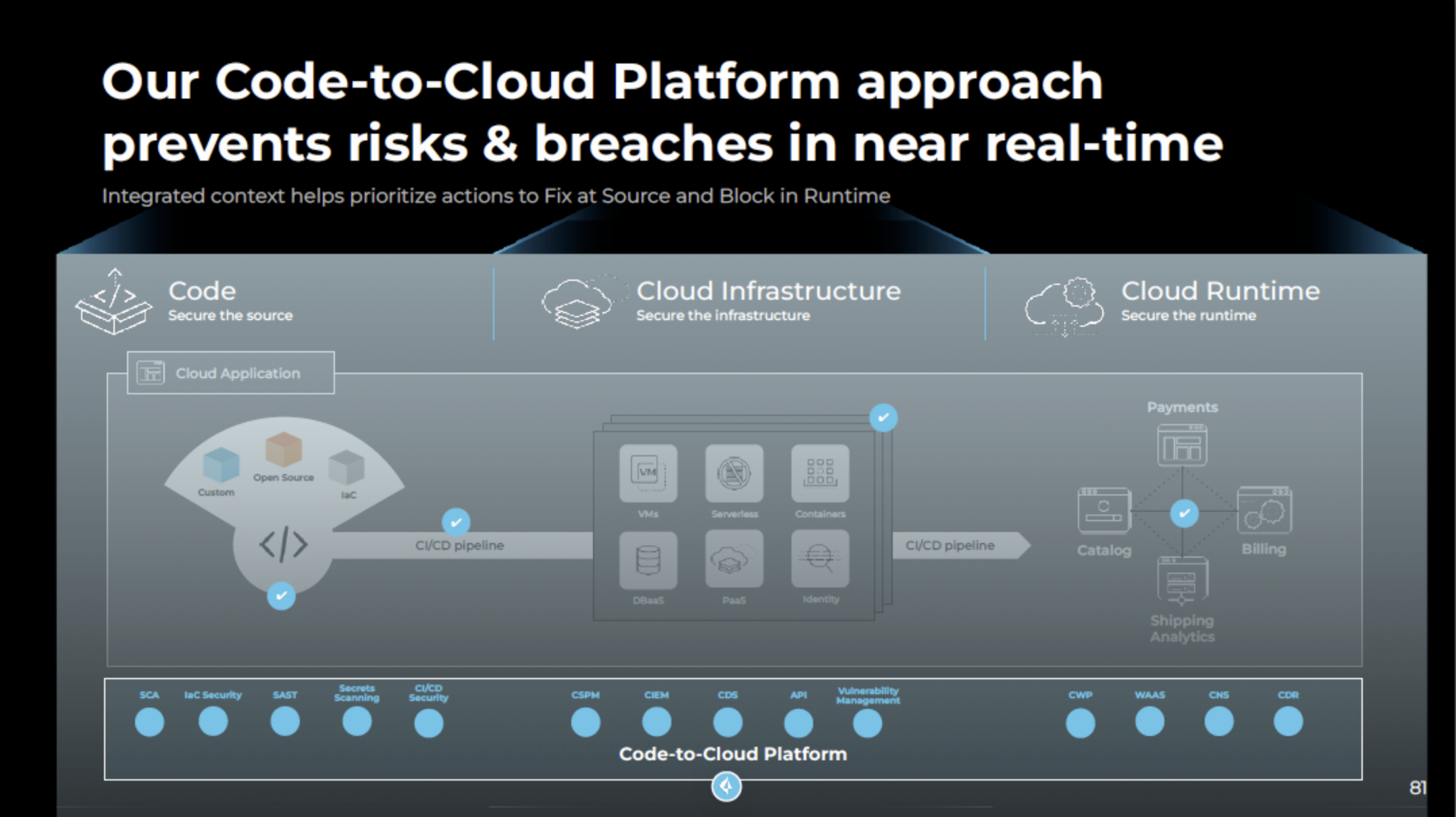
Prisma Cloud began as a cloud security platform, kicked off by the 2018 acquisitions of Evident.io and RedLock. The combination of building and buying on the application security side (including recent acquisitions of BridgeCrew and Cider) have extended Prisma Cloud into CNAPP and beyond.
How is their code-to-cloud strategy working out? On the FY23 earnings call, Nikesh Arora shared that Prisma Cloud has now surpassed $500 million ARR since its initial launch in May 2019. Zero to $500 million ARR in under five years a phenomenal growth, exceeding total ARR for several other public cybersecurity companies.
There's still a long way to go before a clear winner of the CNAPP market emerges — or if the CNAPP market fully materializes in the first place. Many of the best companies in cybersecurity are competing for this market. It's definitely one to keep an eye on.
AI's role in security operations (and beyond)
The spiciest point of view discussed on Palo Alto Networks' FY23 earnings call was the role of AI in security operations. This topic also happens to be one of the most important in our entire industry, so let's dive in.
"The human-driven SOC architecture doesn't work" could not be a more clear indicator of where Palo Alto Networks stands on the current state of things:
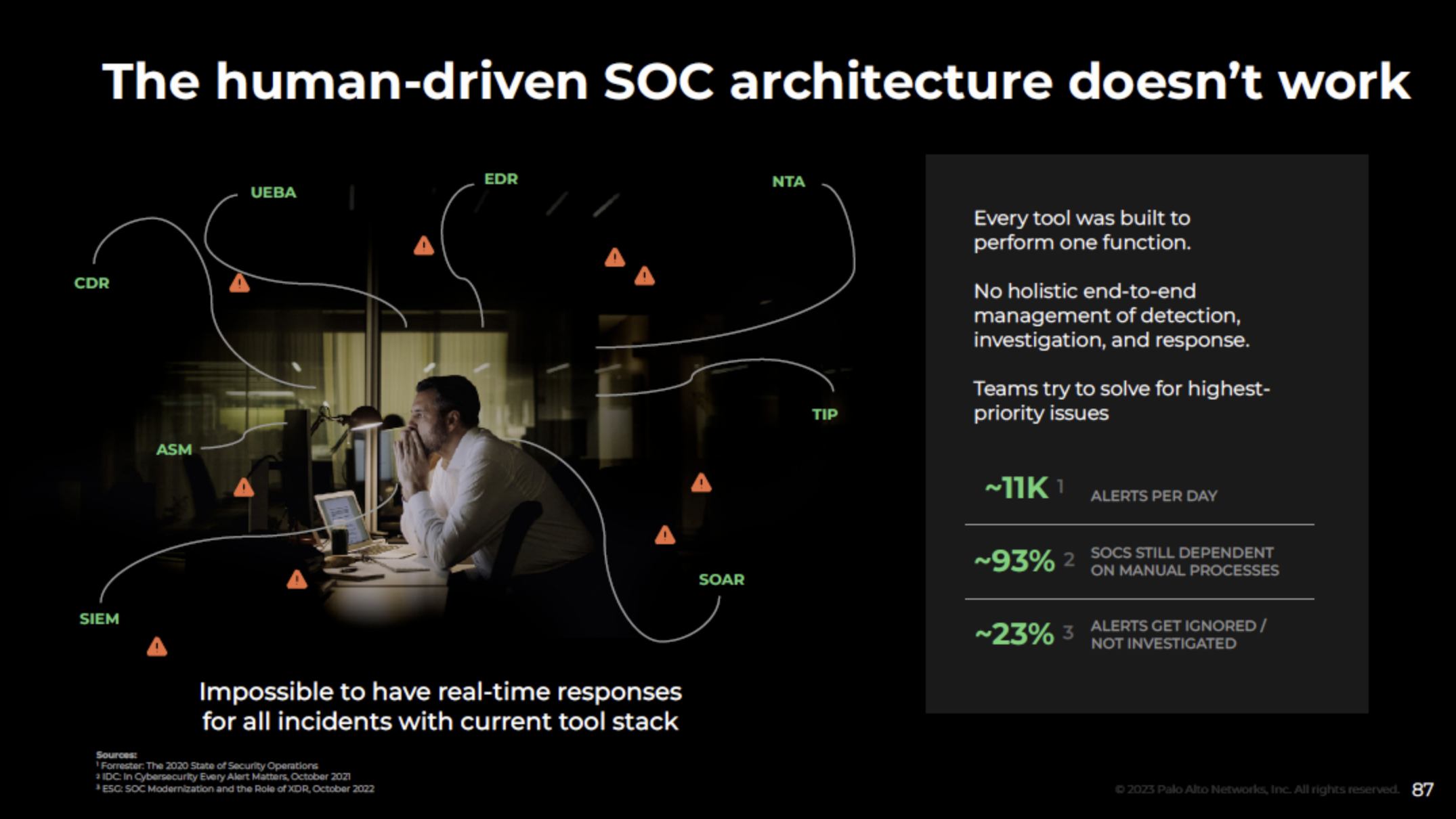
Here's more color commentary, straight from Nikesh Arora:
...the biggest opportunity is...security operations and automation because we think the current paradigm is broken. The current paradigm is a reactive security paradigm. It's the paradigm we say, let's hire three more million people to solve security problems.
No, I don't think that's going to solve the problem. What's going to solve the problem is: Let's collect good data. Let's analyze good data. Let's find out the anomalous behavior. Let's block it while it's happening, so our customers have a better security outcome. I think that's where we're going to be going.
...
A future that is driven by software capability, a future that's driven by software solutions with security, and a future which has integration as a key tenet with the objective of delivering a real-time autonomous security outcome. That's where we think the world is going, that's where we'd like to be, and we think we're best positioned in the industry to be able to deliver that future. Not only that, to deliver great security outcomes to our customers.
How's that for a hot take? The notion of an autonomous SOC was widely criticized when Palo Alto Networks announced their Cortex XSIAM platform in February 2022.
Taken literally, the idea of fully automated security operations could seem far-fetched. On the spectrum of beliefs about automation, I'd call myself a realist. I made the case for a framework to help guide decisions about automation in an article with Tessian shortly (and coincidentally) before Cortex XSIAM was announced:
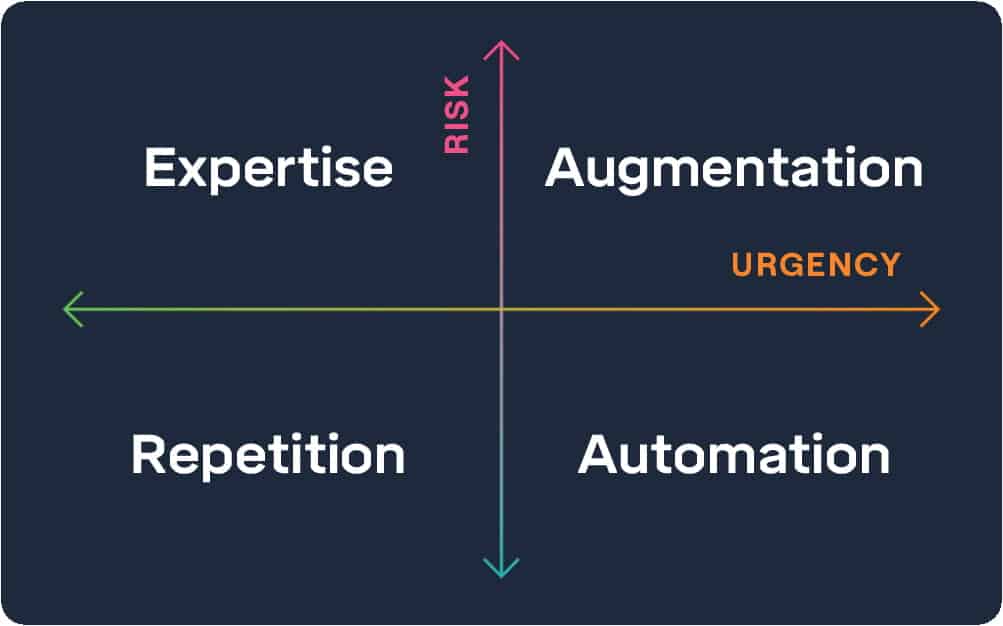
XSIAM fits the model perfectly. It's a balance of augmentation and automation, depending on risk:
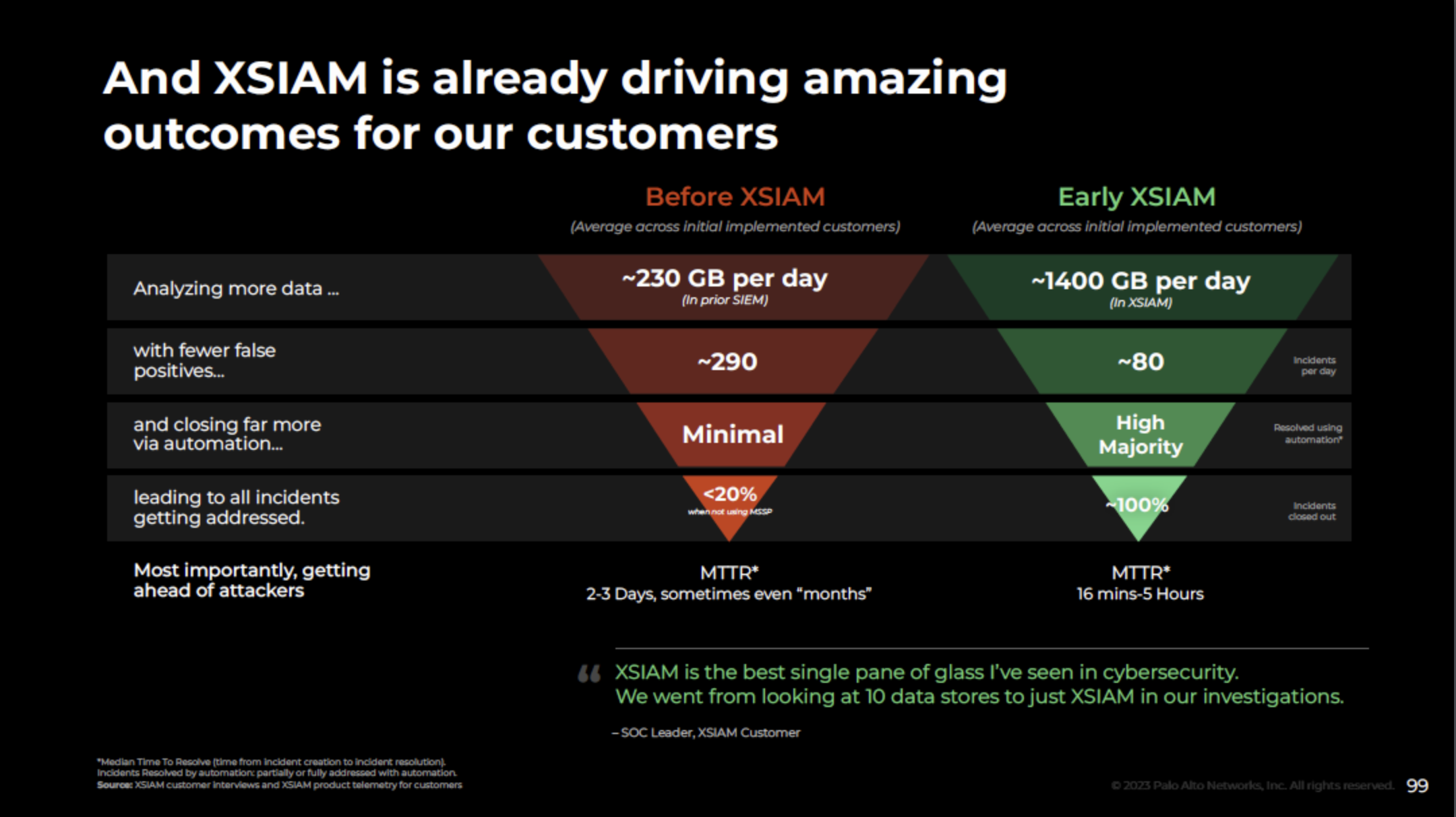
Automation is used up front to analyze more data and evaluate relevance. Lower risk incidents are triaged automatically. Higher risk or unknown incidents move up into the augmentation quadrant. They're evaluated by humans with the assistance of technology to improve the speed and accuracy of the investigation.
The combination of automation and augmentation increases coverage (a higher percentage of incidents are addressed) and greater speed (MTTR is reduced from days/months to hours). This example is a best case scenario, of course, but it's a scenario that needs to become reality far more often.
From a business standpoint, the best anecdote I can give to disprove the skeptics is, "show me the pipeline." It's the exact line a former cybersecurity practice leader at PwC used to give when bright, new ideas (often half-baked) were put in front of him. If you couldn't show a tangible pipeline of customers who wanted the potential offering, it wasn't happening.
So, Nikesh... show me the pipeline. Here's the response to this thought exercise, straight from the FY23 earnings call:
We launched XSIAM to general availability last October and set an aggressive goal of booking north of $100 million in our first year. The year is not over yet. We have closed out the year achieving $200 million in XSIAM.
This is strong validation that our outcome-based value proposition on XSIAM is resonating well with security organizations and also a sign that interest in applying AI to transform security operations is very high.
XSIAM is shaping up to be our fastest-growing offering outside our original next-generation firewall releases. XSIAM transactions are large and long term, which helped to further our goal of evolving our customer relationships from vendor to partner.
How's that for pipeline?! Perfect answer. Zero to $200 million of bookings in less than a year is nothing short of incredible. Especially while the company was continuing to build two other billion dollar businesses and a half-billion dollar business in parallel.
Why did the explosive growth of XSIAM happen? Part of it is the promise of automation. Customers are betting on potential. Revenue is one of the best proxies we have for judging progress, and cybersecurity buyers are voting with their wallets.
We're still early in the journey of transforming security operations with automation. If year one of XSIAM is a sign of what's to come, we could be in for a complete transformation of security operations.
Shifting from selling products to partnering on solutions
The biggest breakthrough shared on the call may also seem to be the most mundane: the company's shift in thinking about go-to-market and moving from selling products to partnering on solutions.
Don't let the simplicity of this transition fool you. It's incredibly difficult to execute. If successful, the implications could be more impactful than any of the flashier topics.
Here's a summary of the GTM transformation shared on the call, shared by BJ Jenkins:
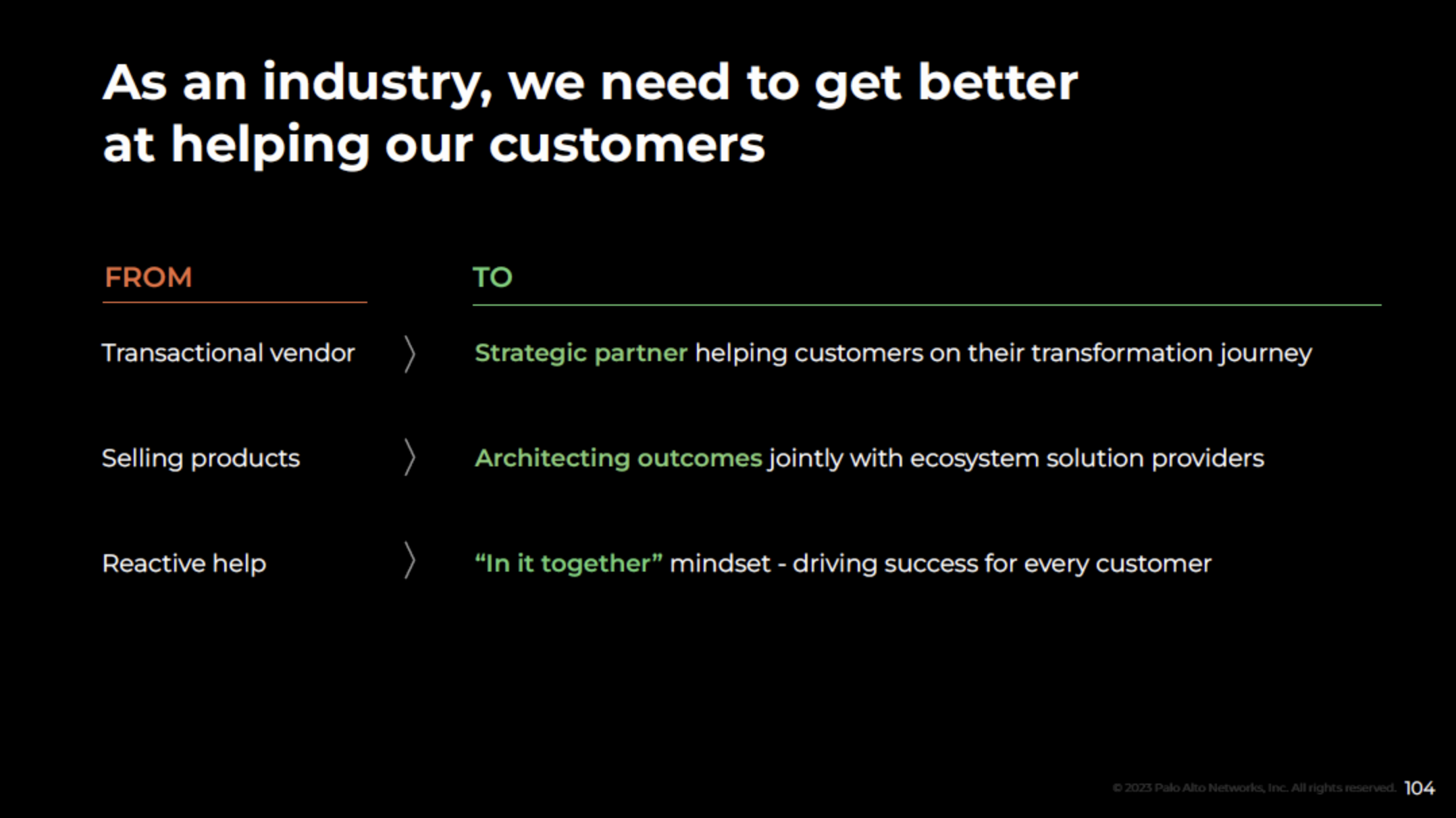
Jenkins' point of view is relatively straightforward to understand. It's deceptively profound when you start thinking through the nuances of what it takes to implement and the potential impact if successful.
Most cybersecurity product companies are transactional and everything else on the "from" side of the list above. They sell products and leave it to customers to figure out how the product fits into the strategy and architecture of their respective security programs.
Good professional services firms take the opposite approach. They're strategic partners to clients, and everything else on the "to" side of the list above. They co-create the strategy and transformation journey alongside clients. As part of the strategy, they architect outcomes. Only then do they get into tactics like vendor selection, implementation roadmaps, and everything else required to deliver outcomes.
The difference in approaches is the reason revenue for large professional services firms like Accenture, PwC, Deloitte, and others is orders of magnitude larger than 99% of cybersecurity product companies. The best professional services firms are world-class at helping their customers.
There are many reasons product companies struggle to become strategic partners and focus on outcomes. One of the biggest constraints is having the scale and breadth of products to properly architect outcomes and capture enough of the value to make the effort worthwhile.
Creating a good strategy, a plan for implementing it, and executing well enough to achieve good outcomes is incredibly difficult — something that's hard to appreciate unless you've done it. The size and scope of an enterprise security initiative is often so large that a single point product is barely a blip on the radar. When you're on the side of the point product, it's challenging to be viewed as a strategic and have your voice be heard by the customer.
This is the reason it's difficult to architect outcomes if you're a point solution with a single product. Scaled, multi-product companies like Palo Alto Networks are more capable of architecting outcomes because they have dozens of products and extensive partnerships. They capture more of the value from the outcomes they help architect. It's possible because they have a lot more they can bring to the table, which means customers are more likely to view them as a strategic partner.
A visual from the Palo Alto Networks presentation does a nice job of explaining both the concept and the opportunity:
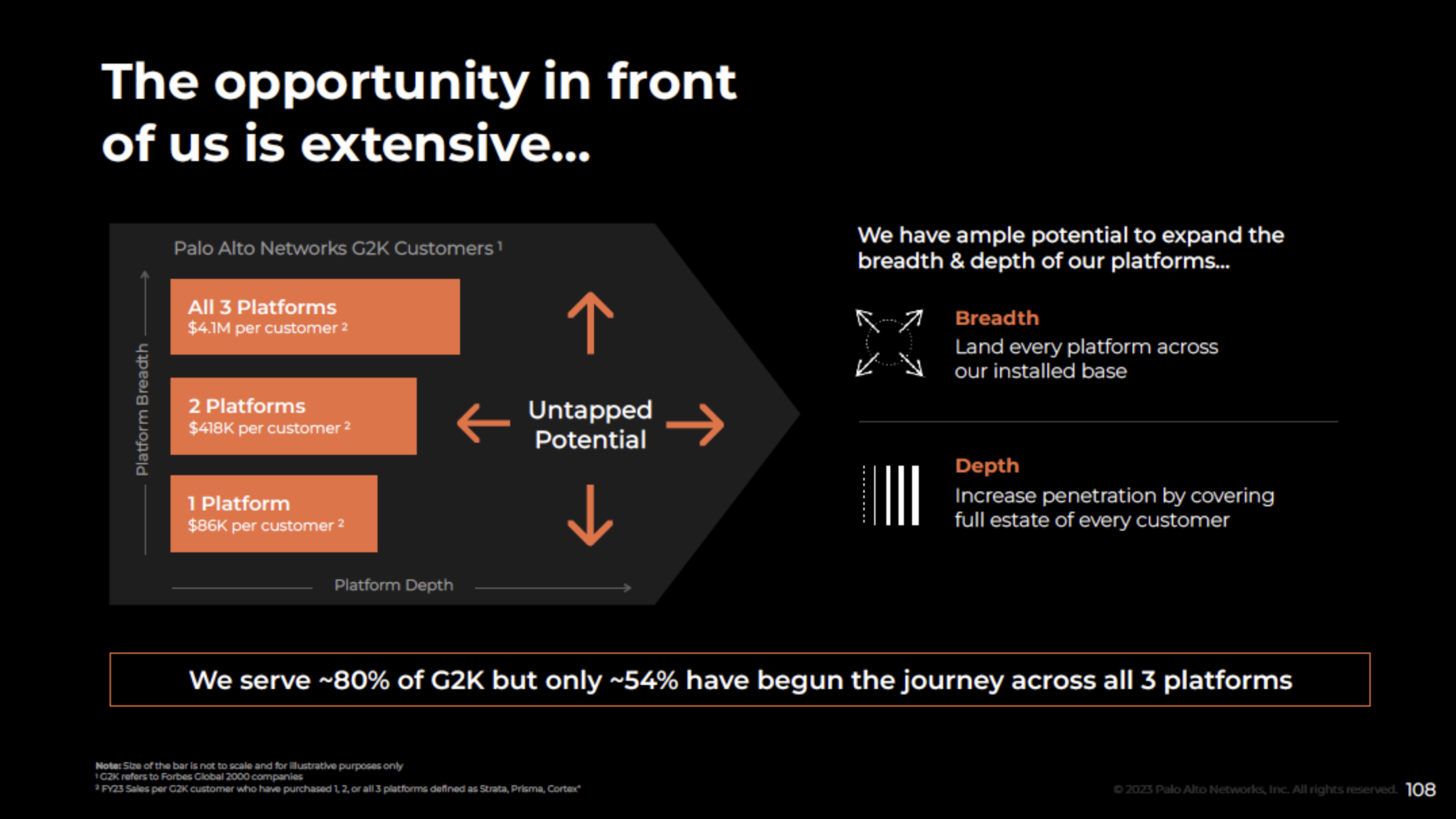
Expansion of breadth and depth ("land and expand") is the outcome every cybersecurity product company wants. Transitioning from selling products to partnering on solutions is how to get there. If Palo Alto Networks is successful, their reward is a significant financial return and a level of customer value rarely seen in the industry today.
What happens if ubiquitous platformization and real-time security outcomes become reality
If big ideas like ubiquitous platformization and real-time security become reality, it likely means several major feats in cybersecurity have all been achieved:
-
An integrated cybersecurity platform with multiple category-leading products within it
-
Demonstrated value and improvement of security outcomes from a unified data layer
-
Meaningful progress in the breadth of coverage and rate of automation for security operations
The future of Palo Alto Networks isn't a consolidation story. It's much larger and more difficult to achieve. And the end state is far more defensible. Platformization is the long, hard road through thoughtful product strategy, integration, and application of new AI and ML superpowers to domain-specific problems.
The problem space and target customers are distinctly enterprise, at least for now. Small and mid-market business segments will likely continue stitching together point products, especially when the products already have pre-built integrations with each other.
It's possible we could see platformization play out on a smaller scale within different customer segments and product categories. You could argue companies like Okta are already doing this today in identity. Cyvatar (mid-market and SMB), Agency (businesses and individuals), and others are doing the same across different customer segments.
Real-time security is starting to happen, too. The rise of "[X] Posture Management" and "[X] Detection and Response" domains like Cloud Security Posture Management (CSPM), Identity Threat Detection and Response (IDTR), and others are leading indicators of a new wave of real-time security products.
Eventually, products like these are going to mature from nascent, emerging categories to the way everyone does security. Real-time security is inevitable — the only uncertainty is how long it will take us to get there.
What happens to Palo Alto Networks if ubiquitous platformization and real-time security outcomes become reality? They become cybersecurity's first $100 billion company.
Their FY23 earnings call was a grand public rendition of the plan to get there. The success of Palo Alto Networks over the past five years has put them in a rare position to capitalize on advantages only possible at the scale and momentum they have today. Successful or not, they've raised the bar for all of us in the cybersecurity industry.



