A new era of access governance is upon us, and BalkanID is one of the companies who is making it happen. On May 12, 2022, BalkanID emerged from stealth, announcing its new Identity Governance and Administration (IGA) platform and $5.75M in seed funding.
It's an interesting time in this part of the cybersecurity ecosystem. IGA has been relatively stable within the five years following SailPoint's 2017 IPO. Since then, SailPoint has commanded the market with relatively few attempts at competition.
That's starting to change in 2022. A slew of financing and M&A activity in IGA signals new competition and potential reshaping of the IGA market and beyond:
-
SailPoint was recently acquired by Thoma Bravo.
-
Outside of the traditional IGA space, CrowdStrike and SentinelOne both made acquisitions in the adjacent Identity Protection market.
-
BalkanID emerged from stealth and announced its seed round.
-
Pathlock raised a $200 million growth round and immediately used it to acquire two companies and merge with two others.
Game on! With all of this activity and the launch of BalkanID, a brand new startup, it's a good time to take a look into IGA and sort out exactly what's happening here.
Today, we're going to narrow our focus even more and take a deep dive into access governance through the lens of BalkanID. To me, this approach feels like seeing the problem space and market through a fresh set of eyes. A few topics we will cover include:
-
The Grind of Access Governance: What's hard about access governance today and where we currently stand as an industry.
-
Revisiting Access Governance: Why access governance needs a revisit, and how BalkanID is going about it.
-
Moving From Regulation-Driven to Security-Driven Access Governance: How changing incentives can change an organization's approach to access governance.
-
Access Governance Is Going AI-First: The need for augmentation in gccess governance, and why this market is ready for an AI-first company.
-
The Future of Access Governance and BalkanID: A long-term view about where the market is headed and how BalkanID fits in.
It's time for a fresh look at one of the most foundational (and painful) topics in cybersecurity. Let's get going.
The Grind of Access Governance
First, let's just call a spade a spade: access governance is a grind. Executing access reviews quarter-over-quarter for years on end is incredibly tedious — a Sisyphean task, if there ever was one.
In the era of regulatory-driven compliance, periodic user access reviews have been the primary mechanism for carrying out access governance. Access reviews work like this:
-
Companies perform risk assessments of applications and infrastructure, along with the entitlements within them, to identify in-scope systems and high risk access.
-
Every quarter (or annually...some pre-defined time interval), access review campaigns are kicked off. Multiple reviewers spring into action (or get dragged into it by their compliance teams) and spend hours reviewing, approving, modifying, or denying access to in-scope systems.
-
Once completed, auditors verify the results to make sure the decisions made by the reviewers are accurate and basic mistakes aren't made — things like disabling access for terminated employees or giving the CFO administrative access to production.
IGA platforms help ease the burden for larger enterprises that have the means to implement and use them. Entitlement data is automatically synced, and access reviews happen via pre-defined workflows. Less fortunate companies are relegated to spreadsheets, manual processes, and Jira tickets — another layer of tedium on top of an already monotonous job.
Regardless of the approach a company takes, a knowledgable human reviewing and approving or denying access is both a laborious and necessary part of the process. Judgment is required to know whether the access someone has is appropriate or not.
From an ecosystem perspective, access governance is an under-served problem space in cybersecurity. Yes, SailPoint is a nice product and successful company. Many other companies have also been offering access governance products for years. These products do the job for compliance. However, let's take a step back here and ask ourselves the hard question: are they really improving security?
If we're being brutally honest with ourselves, the answer is no. A recent report by the esteemed Unit42 at Palo Alto Networks found that 99% of cloud users, roles, services, and resources had excessive permissions. Ultimately, this and other identity-related factors led to misconfigured identities causing 65% of cloud security incidents. Other reports like Verizon's Data Breach Investigations Report have reached similar conclusions.
To be clear, that observation is nothing against SailPoint or any other access governance product on the market today. Access control is just a devastatingly difficult problem to manage that far exceeds the capabilities of most humans who manage it.
If people have to be involved in access governance, how do we make it more enjoyable and effective for them to carry out the task? We'll get to that in the next section.
Revisiting Access Governance
As BalkanID CEO Subbu Rama said when I spoke with him, "access governance needs a revisit." I wholeheartedly agree, as evidenced by the few hundred words I just spent commiserating about the current state.
Convincing someone that access governance needs a revisit isn't that difficult or interesting, though — especially anyone who is routinely on the receiving end of an access review. The more interesting part is how to go about revisiting access governance. That's what we're focused on in this section.
There are three important distinctions to make about exactly what BalkanID does and the customers they focus on:
-
The product is focused on the identity and access governance side of the equation, not management (yet).
-
Integrated applications for access reviews are focused on commonly used SaaS applications and cloud platforms, not on-premise access (this is still supported via API integrations or CSV uploads, though).
-
At this stage of the company, their ideal customer is mid-market companies with 250 employees or more.
These may seem like odd choices. However, a narrow(er) focus on product, integrations, and customers is important — especially for an early stage company.
Why? Access governance isn't actually narrow at all. A startup and its product could become very large doing this alone, especially at enterprise scale. To solve the problem (and build a big company in the process), a startup needs to start with a logical subset of market and features and expand from there.
The answer for how to revisit access governance is not "people need to work harder and do a better job at access reviews." Rubber-stamping definitely happens, but let's be empathetic and focus our blame on the problem, not the people.
The problem is that managing and reviewing access is too hard. There is too much data and information for any reasonable person to handle. That's where better tools come in — they need to augment humans and make the job easier. Executing this grandiose vision at a tactical product level is the key to progress in this area of the cybersecurity ecosystem. It's also an opportunity to unlock a deceptively large market.
I've been exploring the topic of access governance for a long time. Nearly a decade ago, I was the anonymous subject of a TechCrunch article written by Nir Eyal. Nir is an expert on behavioral design and habit-forming technologies. The article was based on a conversation we had about how to incentivize people to do things they don't want to do.
When posing my dilemma to Nir, the specific example I gave was... you guessed it: access reviews. The entire article is worth a read because it details his recommendations step-by-step. In case you're short on time, we'll walk through the main points here and connect the dots with what BalkanID is doing.
At an abstract level, tasks like access reviews (and anything under the umbrella of access governance, really) are an act of convincing others to do uninteresting tasks. In our case, access reviews are infrequent and involve work done outside normal responsibilities. The article makes three specific recommendations to improve results for this type of task.
First, stage tasks into conquerable chunks. Progressive disclosure is the fancy, formal term for this. Traditional access reviews often bury reviewers with spreadsheets that are thousands of lines long. BalkanID is far more dynamic. It's incredibly simple to kick off a focused access review on the fly based on a powerful set of filters.
Second, demonstrate progress. People want to know when the pain will end, and they want it to hurt less the next time. BalkanID uses a combination of expert systems and artificial intelligence to incrementally train the system each time an access review is completed. The next time around, everything becomes smarter and more accurate: identifying outliers, flagging high risk access, identifying account ownership, and more.
Finally, reinforce good behaviors with autonomy and rewards. Part of this recommendation is an organizational change. BalkanID isn't going to hand out bonuses or happy hours — that's up to you. However, it does give users the autonomy to explore access, export data for special purpose projects, and slice and dice reporting however you like. The product is more like a business intelligence platform than a security tool.
Although the recommendations seem simple, putting them into action is a significant responsibility. As the article concludes:
It is the job of the person inflicting the pain to do their utmost to ease it. Not doing so is intellectually lazy... Considering how the receiver could more easily comply with the request is at the heart of inspiring action.
Thoughtful design is a core part of the user experience for BalkanID. There is a distinct and obvious difference between products designed for the way things should work versus how things actually work. BalkanID is clearly building towards the latter — an access governance product designed for the way people want to use it.
Moving From Regulation-Driven to Security-Driven Access Governance
In addition to the micro-level psychological and product nuances we just discussed, an important macro-level shift is underway. The move from regulation-driven to security-driven access governance is changing the strategic drivers, incentives, and approach in this part of the ecosystem.
Nipun Gupta recently posed an important question about the role of regulations as the driver of security outcomes:
Such an important yet unique point of view - while regulations were considered a driver once, have they become an inhibitor in achieving practical cyber security outcomes?
— Nipun Gupta (@nipungupta) May 10, 2022
What do you think? https://t.co/8YyUESpeeE
While the overall answer is nuanced, regulations have reached a point where they are inhibiting the actual security outcomes we want to achieve with access governance.
Few companies would voluntarily do manual access reviews if it wasn't mandated by one or more regulations or compliance requirements. Going from nothing to something is a good thing, but it's also far from an ideal state.
The true outcome we want from access governance is to make sure people have exactly the amount of access they need and nothing more. Put formally, entitlement sprawl is the problem, and least privilege is the objective.
Periodic access reviews are the mechanism we've historically used for (trying to) address the problem and meet the objective. However, there is a huge gap between simply completing an access review and doing it well. Here's the reality:
-
The way it actually works: Look at in-scope systems, make sure terminated employees don't still have access, double-check administrative roles, move on.
-
The way it should work: reviewers look across all enterprise systems for deviations and excessive access based on a person's day-to-day job responsibilities, reducing unneeded access and refining application roles where needed to achieve least privilege.
Access reviews are just a means to an end. If the objective isn't being achieved, it's time to change the means.
That's exactly what is happening. Forward-thinking CISOs have realized compliance-driven access reviews aren't reducing their overall exposure and risks created by excessive access. Compliance hasn't caught up yet, so access reviews still need to be done. However, companies are proactively taking action.
Identity protection is an emerging area of the cybersecurity ecosystem — a direct result of companies proactively seeking out and remediating access-related risks. CrowdStrike and SentinelOne have both made major identity protection acquisitions within the past year. I analyzed these moves in detail when recapping annual earnings for both companies:
Bigger picture, CrowdStrike and SentinelOne may have finally figured out how to incorporate useful identity analytics into a product portfolio (and their customers' security programs). This has been an elusive need in the industry.
SentinelOne CEO Tomer Weingarten nicely summarized the outcome both companies are seeking with their identity protection products:
Attivo, as part of SentinelOne, will help organizations reduce their attack surface not only at the device level but now at the human identity level, too.
A similar objective as access governance, but much more proactive. Organizations aren't going to wait around for quarterly access reviews of regulated systems to ...hopefully-maybe-fingers-crossed... clean up excessive access. They're going to hunt it down and fix it. That's what reducing the attack surface at the human identity level means.
When analyzing the acquisitions by CrowdStrike and SentinelOne, I made an observation about identity protection being a missed opportunity for traditional Identity and Access Management (IAM) companies:
Identity protection seems like it could have been a logical product extension for Identity and Access Management (IAM) companies. Companies like SailPoint have kinda-sorta been working on identity analytics products for a while. For whatever reason, the products didn't stick with customers yet — too early, perhaps?
We're still in the early innings of identity protection, though. A miss by later-stage companies is an opportunity for BalkanID to correct and capitalize on. That's exactly what Subbu Rama is seeing with early customers. While access reviews are an obvious and primary use case, some customers have been more interested in features that allow them to freely discover and eliminate excessive access.
Discovering entitlement sprawl goes well beyond compliance. It used to be something security professionals knew and never wanted to talk about. Now, it's a necessary part of security, not just an annoying compliance exercise we do every quarter. BalkanID is giving us the tools we need to be compliant while also digging in to do the difficult, security-driven work.
Access Governance Is Going AI-First
Now that we've covered both micro-level techniques and macro-level trends for access governance, it's time to tie everything together and talk about how companies like BalkanID can make all of this possible.
In my article about The Rise of Security Augmentation for Human Layer Security, I proposed a few criteria that make tasks a good fit for augmentation:
Tasks that are both high risk and high urgency should be augmented using a combination of human intelligence and machines. This is the area where both speed and quality matter. Any gains in speed from machines or judgment from humans can make a big difference.
Visually, various tasks can be plotted within this framework to help determine the type of approach we should use:
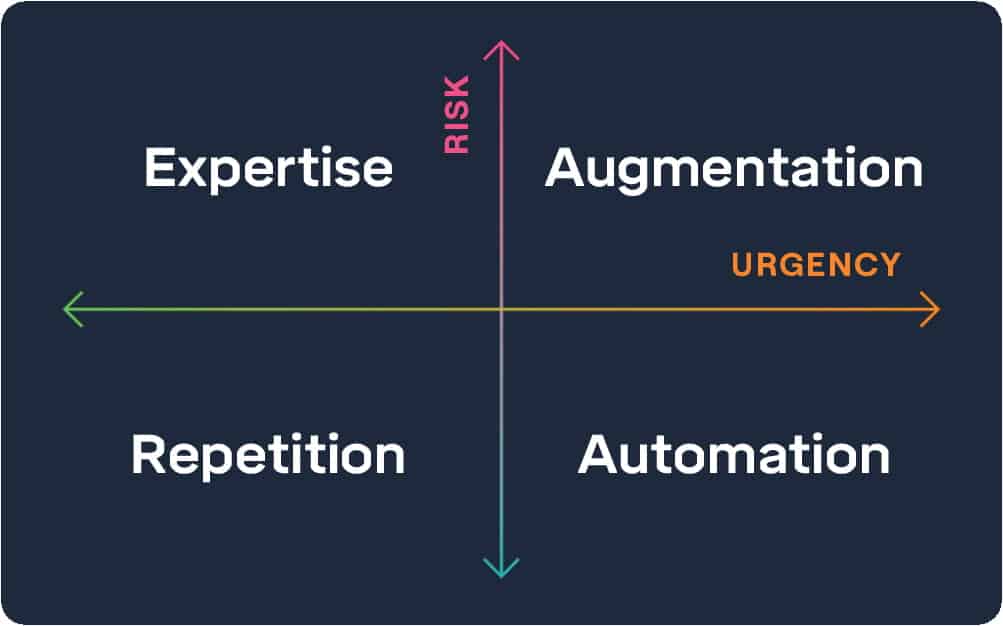
Access governance is an obvious candidate for augmentation. Excessive access is high risk — as we discussed earlier, it causes most cloud security incidents. The work to reduce excessive access has become high urgency.
We need to augment humans and increase the speed and quality by which they can find and remediate excessive access. Subbu Rama shared a great thought exercise to explain the challenge of effective access governance without augmentation:
Let's say we have 1,000 employees in a company and 10 SaaS applications. This is very small, but even with 10, you're now looking at 10,000 entitlements. Obviously, you cannot review all of them.
This is exactly the problem with access governance at scale. The math starts working against us quickly. It doesn't take long for the task to become unmanageable.
People need help. That's where AI-driven augmentation comes into play. For example, BalkanID uses AI to prioritize the access a reviewer truly needs to look at and highlight potential outliers. There are many other examples just like this one. The potential use cases for augmentation can go on and on.
For the next generation of access governance products, the objective is to drastically increase the level of augmentation and iteratively move towards automation as products, processes, and data mature. Bigger picture, the way we'll get there is as philosophical as it is technical: we need AI-first companies in Identity Governance and Administration (IGA).
This isn't marketing or hyperbole. Artificial Intelligence has reached a point where it can (and should) be applied to problems like access governance. Companies takling this problem space today have the advantage of building their products on top of AI infrastructure from cloud providers from day one. They don't need to build AI — they need to apply AI to solve specific challenges in this domain.
Starting as an AI-first company from inception is a meaningfully different approach to building a product than the previous generation of IGA products. The product turns out differently when it's built with AI front and center instead of being added on later — sometimes ten years later.
This is exactly what Subbu Rama is doing with BalkanID. Right now, it's an early stage company. Near-term, this means an intense focus on using expert systems to configure and train the AI-based models behind the BalkanID platform. It's impractical to turn everything over to a deep learning model and expect it to work. Instead, they're going through the rigorous process of calibrating the system to minimize false positives and false negatives.
Baby steps matter. Early AI-based features are small but important wins on the long-term road towards the advancement of access governance. To truly reach the outcomes we seek, we need to balance short-term utility and incremental progress with the long-term commitment and investment required to build more sophisticated AI products.
The Future of Access Governance and BalkanID
Despite my optimism about the augmented future of access governance, a dose of pragmatism is needed here: we're on a long road towards realizing the ultimate vision. And that's okay.
In the case of BalkanID, patience and long-term commitment might even be a competitive advantage. The company's founders are all experienced entrepreneurs and executives with pragmatic expectations about the timing and path it's going to take to execute the vision. They've had successful exits and leadership roles in the past. This time, it's about doing the work to make lasting change and building a large company in the process.
I worry about any company who enters the market and says it's going to revolutionize access governance overnight. Nearly 20 years after the company was founded, SailPoint is still converting new customers from legacy IGA solutions and moving their own customers from the on-premise product to cloud. Extra capital from Thoma Bravo might help, but we're on a long, slow path regardless of how much capital gets infused.
What's in store for the overall Identity Governance and Administration (IGA) market in the next few years? SailPoint is going to be busy consolidating the existing market. BalkanID is heading up the new wave of companies that's coming next. I'm excited to follow their journey and growth as the market shakes out and evolves.



